In today's hyper-connected world, securely connecting remote IoT devices through peer-to-peer (P2P) networks using a Raspberry Pi has become a crucial skill for tech enthusiasts and professionals alike. The Internet of Things (IoT) continues to expand at an unprecedented rate, and understanding how to manage and secure these connections is vital for maintaining data integrity and privacy. In this comprehensive guide, we will delve into the intricacies of setting up a secure P2P network with Raspberry Pi, ensuring your remote IoT devices are protected against cyber threats.
This article will walk you through the process step by step, from understanding the basics of IoT security to implementing advanced techniques that safeguard your devices. Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge you need to build a robust, secure IoT ecosystem.
By the end of this article, you'll have access to downloadable resources and actionable tips that will help you confidently deploy and manage secure remote IoT P2P connections using Raspberry Pi. Let's get started!
Read also:Movie Rilz The Ultimate Guide To Latest Movie Releases And Trends
Understanding IoT and Its Security Challenges
The Internet of Things (IoT) refers to a network of interconnected devices capable of exchanging data over the internet. From smart home appliances to industrial automation systems, IoT applications are transforming industries and enhancing everyday life. However, with the convenience of IoT comes significant security challenges.
One of the primary concerns is unauthorized access to IoT devices. Hackers can exploit vulnerabilities in these devices to gain access to sensitive information, disrupt services, or even take control of critical infrastructure. Therefore, securely connecting remote IoT devices is essential to mitigate these risks.
Why IoT Security Matters
- Protects sensitive data from unauthorized access.
- Prevents potential cyberattacks on interconnected devices.
- Ensures the reliability and functionality of IoT systems.
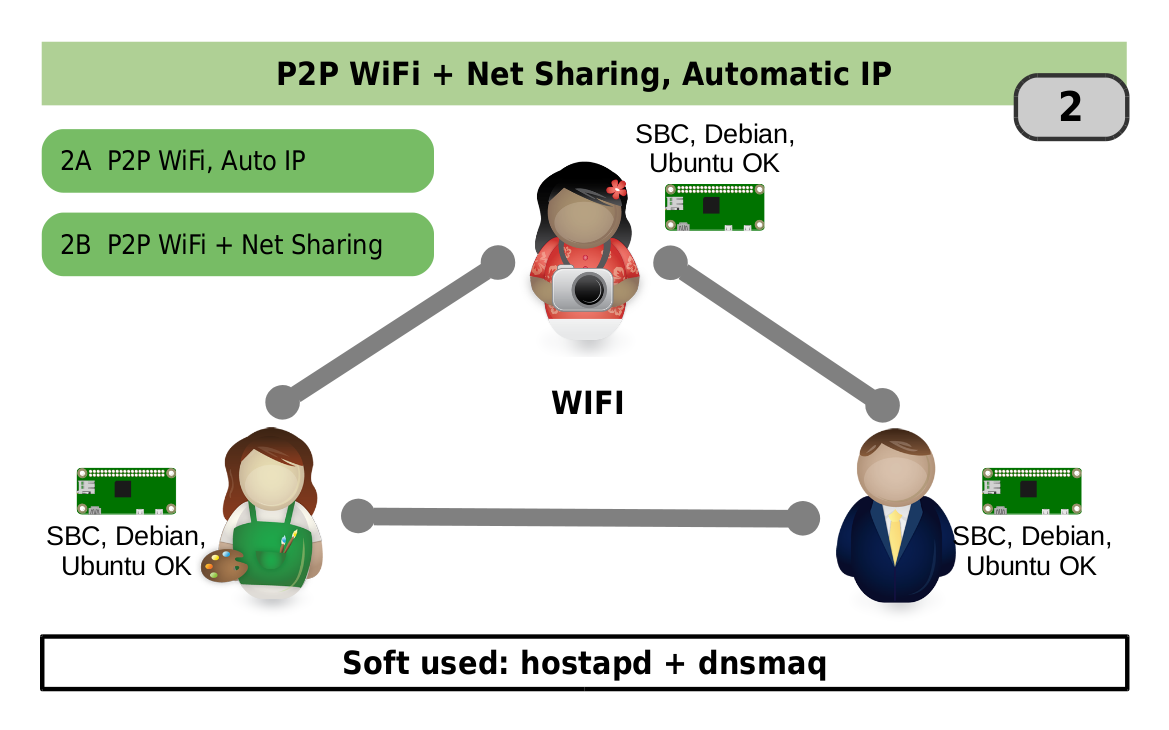
Peer-to-Peer (P2P) Networking Explained
Peer-to-Peer (P2P) networking allows devices to communicate directly with each other without relying on a centralized server. This decentralized approach offers several advantages, such as reduced latency, improved scalability, and enhanced resilience against network failures.
When it comes to IoT, P2P networking can significantly enhance the performance and security of remote device connections. By eliminating the need for a central server, P2P reduces the risk of single points of failure and makes it harder for attackers to compromise the entire network.
Advantages of P2P Networking in IoT
- Increased efficiency in data transfer.
- Lower operational costs due to reduced reliance on servers.
- Improved security through decentralized architecture.
Introducing Raspberry Pi as a Secure IoT Platform
Raspberry Pi has emerged as a popular choice for IoT projects due to its affordability, flexibility, and powerful capabilities. This tiny yet versatile device can serve as a secure gateway for connecting and managing remote IoT devices.
Equipped with various interfaces and supported by a wide range of software tools, Raspberry Pi offers developers the ability to implement advanced security features such as encryption, authentication, and firewall protection.
Read also:New Movierulz Kannada Your Ultimate Guide To Kannada Movies
Key Features of Raspberry Pi for IoT Security
- Support for multiple operating systems, including Linux-based distributions.
- Compatibility with popular security protocols like TLS and SSH.
- Ability to integrate with cloud services for enhanced functionality.
Steps to Securely Connect Remote IoT P2P with Raspberry Pi
Setting up a secure P2P connection using Raspberry Pi involves several critical steps. Below, we outline the process in detail:
Step 1: Prepare Your Raspberry Pi
Begin by installing the latest version of Raspberry Pi OS on your device. Ensure that all necessary drivers and firmware updates are applied to maintain optimal performance.
Step 2: Configure Network Settings
Configure your Raspberry Pi to connect to your local network. Use a static IP address to ensure consistent communication between devices.
Step 3: Implement Security Measures
Enable encryption protocols such as TLS and SSH to secure data transmission. Additionally, configure firewalls to restrict unauthorized access.
Step 4: Establish P2P Connections
Use software tools like WebRTC or libp2p to establish secure P2P connections between your IoT devices and Raspberry Pi.
Best Practices for IoT Security
Adhering to best practices is crucial for maintaining the security of your IoT ecosystem. Below are some recommendations to consider:
Regularly Update Firmware and Software
Keep all devices and software up to date with the latest security patches to protect against emerging threats.
Use Strong Authentication Methods
Implement multi-factor authentication (MFA) to ensure only authorized users can access your IoT devices.
Monitor Network Activity
Regularly monitor network traffic for any suspicious activity that could indicate a potential security breach.
Download the Ultimate Guide to Secure IoT P2P Connections
For a comprehensive resource on securely connecting remote IoT devices using Raspberry Pi, download our ultimate guide. This guide includes step-by-step instructions, advanced security tips, and practical examples to help you master IoT P2P networking.
What You'll Find in the Guide
- Detailed instructions for setting up Raspberry Pi for IoT.
- Best practices for securing IoT P2P connections.
- Case studies demonstrating real-world applications.
Real-World Applications of Secure IoT P2P Connections
Secure IoT P2P connections have numerous applications across various industries. Below are a few examples:
Smart Home Automation
Connect smart home devices such as thermostats, lighting systems, and security cameras using P2P networking for enhanced control and security.
Industrial IoT (IIoT)
Implement secure P2P connections in manufacturing environments to optimize production processes and improve efficiency.
Healthcare IoT
Utilize secure IoT P2P networks in healthcare settings to monitor patient health data and provide timely interventions.
Data and Statistics Supporting IoT Security
According to a report by Gartner, the number of connected IoT devices is projected to reach 25 billion by 2030. With this rapid growth comes increased security risks. A study by IBM revealed that 60% of data breaches involve IoT devices, underscoring the importance of securing these connections.
Conclusion
Securing remote IoT P2P connections using Raspberry Pi is essential for protecting your devices and data from potential cyber threats. By following the steps outlined in this guide and adhering to best practices, you can create a robust and secure IoT ecosystem.
We invite you to download our ultimate guide for more in-depth information and practical tips. Feel free to share this article with your network and leave a comment below if you have any questions or feedback. Together, let's build a safer and more connected world!
Table of Contents
- Understanding IoT and Its Security Challenges
- Peer-to-Peer (P2P) Networking Explained
- Introducing Raspberry Pi as a Secure IoT Platform
- Steps to Securely Connect Remote IoT P2P with Raspberry Pi
- Best Practices for IoT Security
- Download the Ultimate Guide to Secure IoT P2P Connections
- Real-World Applications of Secure IoT P2P Connections
- Data and Statistics Supporting IoT Security
- Conclusion